Secure Coding Practices for Aspiring Ethical Hackers
Introduction Secure coding is the practice of writing code in a way that guards against the introduction of security vulnerabilities. For aspiring eth...
296 articles on cybersecurity tips, tutorials, and beginner guides.

Introduction Secure coding is the practice of writing code in a way that guards against the introduction of security vulnerabilities. For aspiring eth...

Introduction With the proliferation of mobile devices in personal and professional environments, ensuring their security has become a pressing concern...

Introduction Digital forensics plays a critical role in cybersecurity. It's the science of uncovering and interpreting electronic data for use in a co...
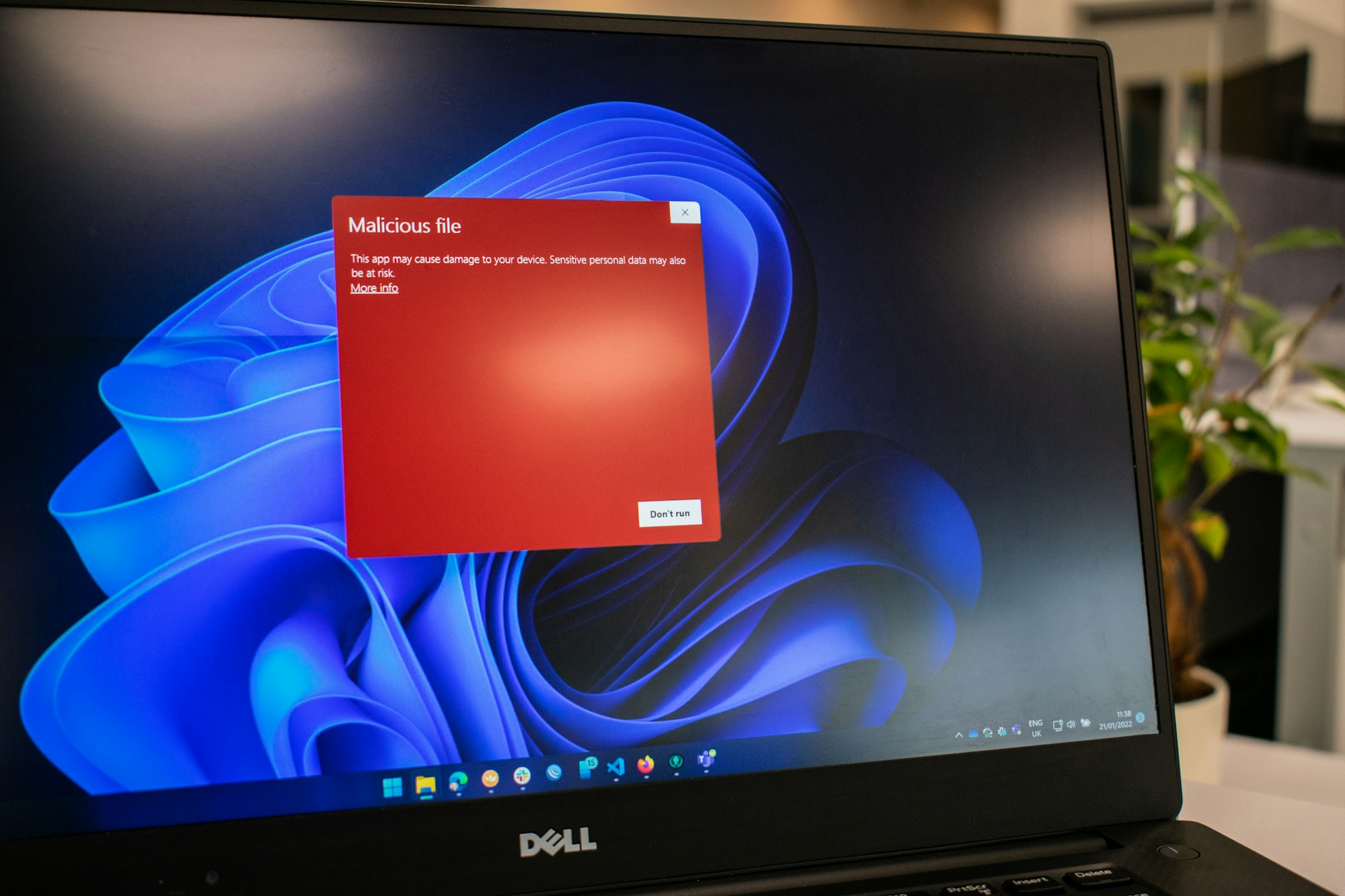
Introduction In the world of cybersecurity, malware stands as one of the most persistent threats. From its early inception in the form of simple compu...

Introduction Social engineering remains one of the most potent tools in a hacker's arsenal. It involves manipulating individuals into divulging sensit...

Introduction In the burgeoning field of cybersecurity, certifications play a critical role in validating one's skills and knowledge. For those startin...
Introduction The Certified Information Systems Security Professional (CISSP) is considered a premier cybersecurity certification worldwide. It is a ri...

Introduction Microsoft's Windows is the most widely used operating system (OS) in the world, particularly in the corporate environment. This prevalenc...
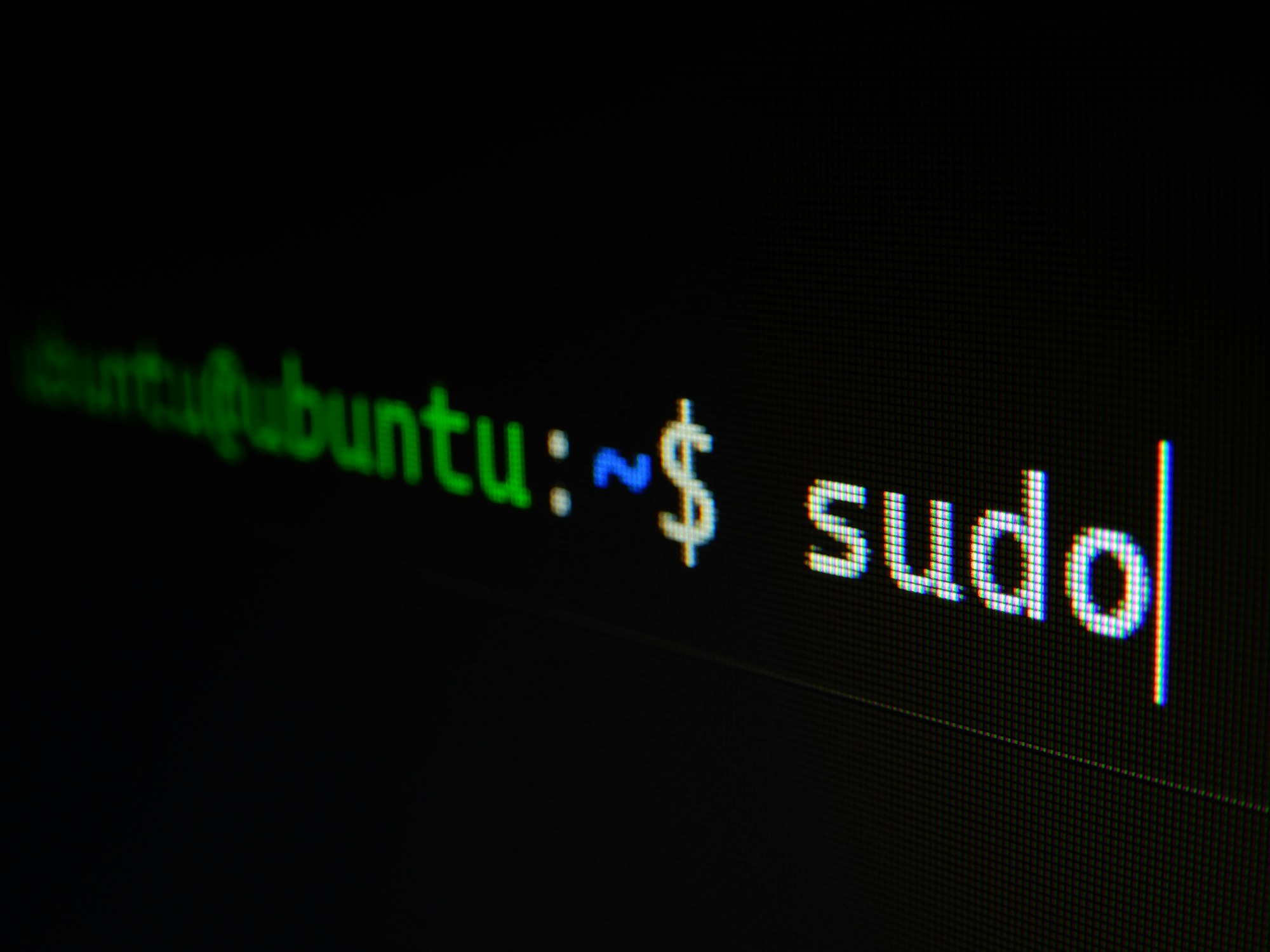
Summary: Explore why Unix/Linux is the preferred operating system for many hackers, and provide a beginner's guide to using Linux for ethical hacking....

Introduction Security architecture and security engineering are critical aspects of cybersecurity. They involve the design, implementation, and ongoin...
Introduction System administration is a key aspect of cybersecurity and hacking. It involves the configuration, upkeep, and reliable operation of comp...

Summary: A beginner's guide to fundamental networking concepts, such as IP addressing, TCP/IP model, DNS, firewalls, and VPNs. Networking is a fundame...