The Parasites of Web Analytics: How Referrer Spam and Malvertising Exploited the Same Internet
Two parallel dark arts of the mid-2010s web that turned advertising infrastructure into attack vectors Executive Summary Between 2014 and 2017, two se...
296 articles on cybersecurity tips, tutorials, and beginner guides.

Two parallel dark arts of the mid-2010s web that turned advertising infrastructure into attack vectors Executive Summary Between 2014 and 2017, two se...

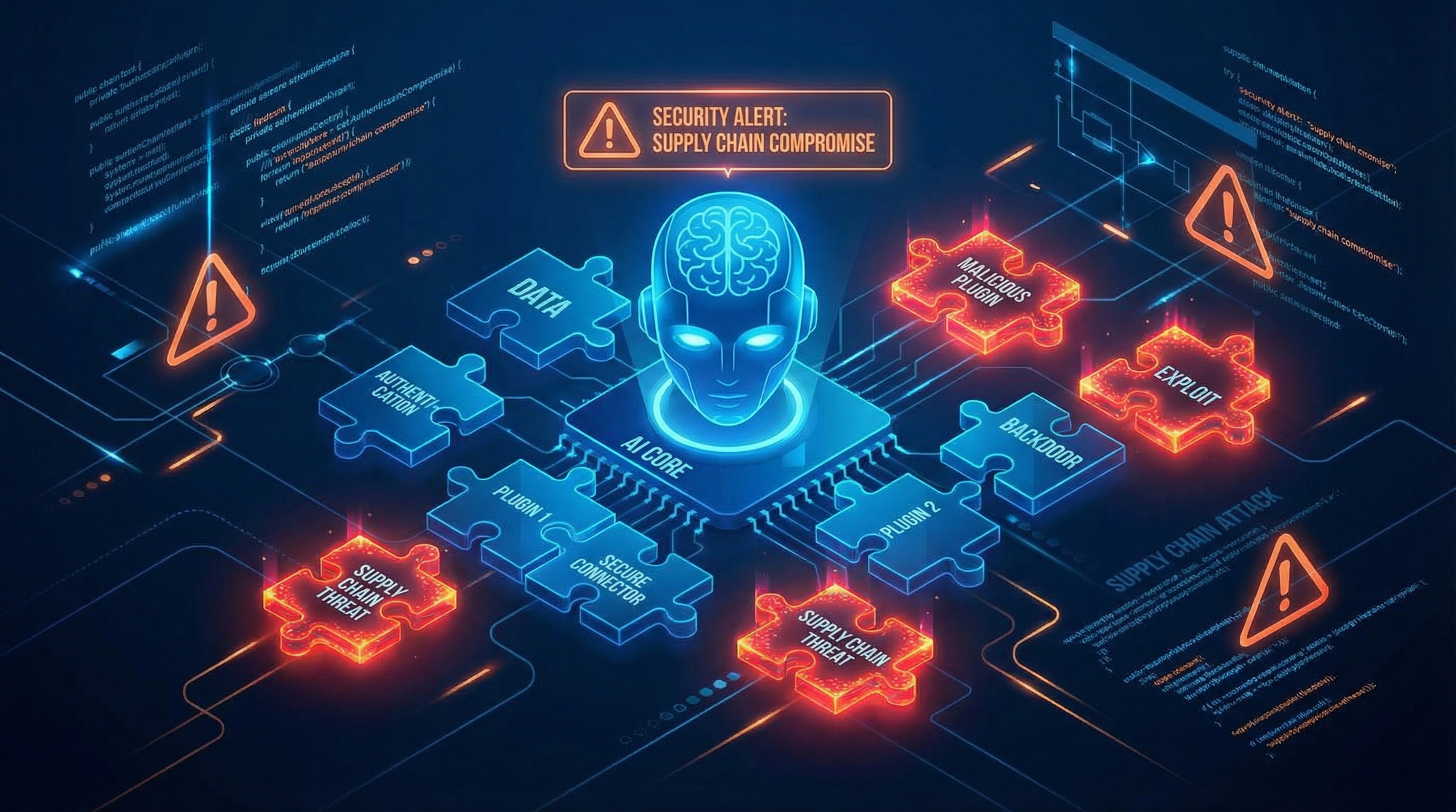
The ClawHavoc campaign is the most alarming AI supply chain attack to date — and most people still don't know it happened. It started with a butler jo...
Artificial intelligence is moving faster than security governance frameworks can adapt. Organizations are deploying large language models into workflo...

🚨 IMMEDIATE ACTION REQUIRED: CISA's remediation deadline is February 16, 2026 —that's tomorrow . If you run BeyondTrust Remote Support or Privileged ...

Published: February 8, 2026 TL;DR: Eight critical vulnerabilities affecting Tenda and D-Link routers were disclosed this week, allowing attackers to.....
And how to protect yourself from the 632 vulnerabilities researchers just found hiding in plain sight TL;DR — Key Takeaways 🔬 First major study: Rese...
Six zero-day vulnerabilities. All actively exploited. One already weaponized since December 2025. And you have until March 3rd to patch them all. If y...

Full disclosure: The AI assistant writing this article runs on OpenClaw. Yes, really. Keep reading. TL;DR: OpenClaw went from 145K GitHub stars to "se...

In the high-stakes world of cryptocurrency security, there's a thin line between catastrophic loss and triumphant protection. A single vulnerability i...

When AI Can Execute Code, Every Injection Is an RCE A comprehensive technical analysis of prompt injection vulnerabilities in agentic AI systems, with...

Executive Summary Google Threat Intelligence Group (GTIG) has identified a new Russian-linked threat actor deploying a previously undocumented malware...

Introduction: The AI Agent Gold Rush Meets Reality Picture this: An AI assistant that cleans up your inbox, manages your calendar, orders your lunch, ...