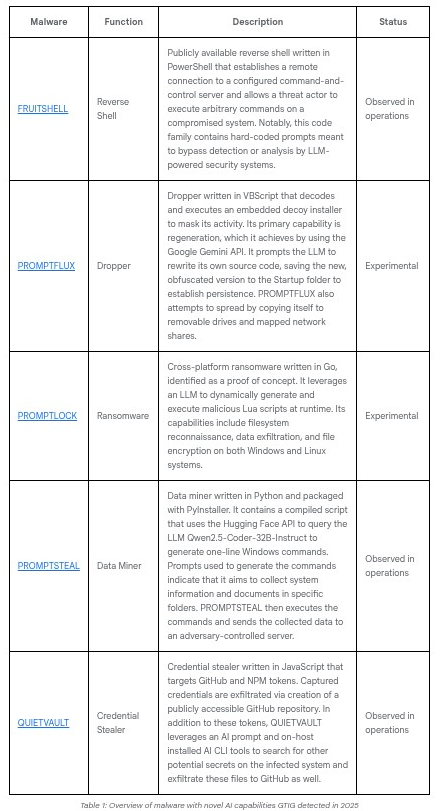
OpenAI Signals Imminent "Cybersecurity High" Threshold as GPT-5.2-Codex Transforms Defensive Security
Sam Altman announces upcoming releases will reach unprecedented AI cyber capability levels, introducing "defensive acceleration" strategy January 24, ...