Apple Is Texting Millions of People About a Hack
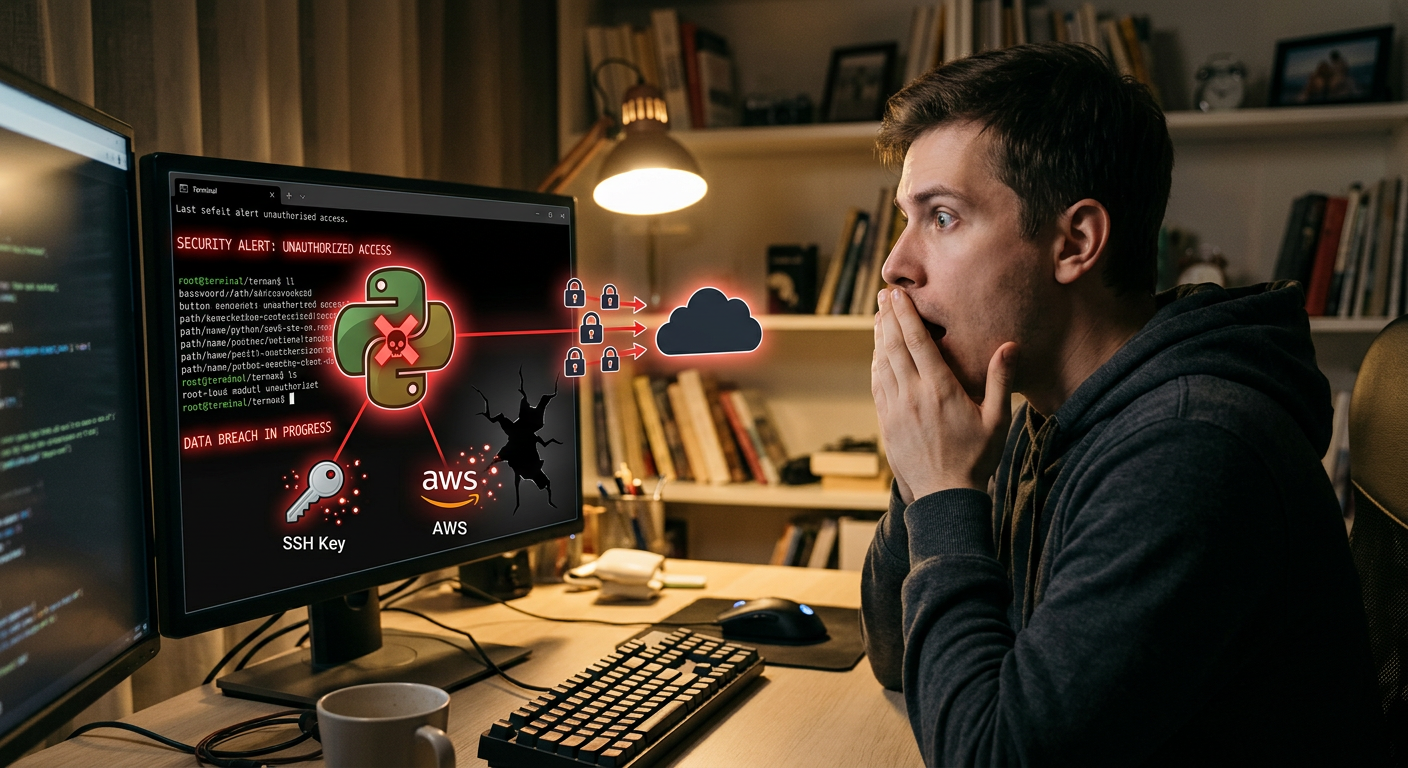
If you’ve seen a lock screen notification from your iPhone’s Settings app warning about “Critical Software” and active attacks — you’re not being scammed. That’s Apple. And it means something serious is happening.
Apple almost never pushes security warnings directly to user lock screens. The last comparable action involved a nation-state spyware campaign. The fact that they’re doing it now — for exploit kits called Coruna and DarkSword — tells you everything about how serious this is.
Here’s what you need to know.
What the Notification Says
Millions of iPhone and iPad users are seeing an alert like this:
“Apple is aware of attacks targeting out-of-date iOS software, including the version on your iPhone. Update to the latest iOS for important security fixes.”
It appears as a push notification from the Settings app — not an app you downloaded, not a pop-up in Safari. It’s coming from Apple’s own notification infrastructure, which means they have enough confidence in the active threat to push it to hundreds of millions of devices.
Two Exploit Kits. One Big Problem.
Two separate exploit kits are being used in active campaigns:
Coruna — Targeting iOS 13.0 through 17.2.1
Coruna is a browser-based exploit kit that targets unpatched WebKit vulnerabilities across a wide range of iOS versions. The attack works like this:
- You click a malicious link — in a text message, social media post, email, or search ad
- The link loads a specially crafted web page in Safari (or any browser using WebKit, which is every browser on iOS)
- Coruna’s exploit chain runs in the background, exploiting a WebKit memory corruption bug
- If successful, it achieves code execution on your device — no app installation required
- From there, attackers can steal data, install persistent malware, or pivot to other targets
Affected range: iOS 13.0 – 17.2.1 Who that is: iPhone 6s, 7, 8, X, XS, 11, 12 users who haven’t updated — potentially hundreds of millions of devices still in active use worldwide
DarkSword — Targeting iOS 18.4 through 18.7
DarkSword is newer and more concerning in some ways: it targets recent iOS versions. If you updated your phone in the last few months and thought you were protected, DarkSword may still apply to you.
The attack mechanism is similar — drive-by web exploitation via malicious web content — but the vulnerability chain targets WebKit issues specific to iOS 18.x branches that Apple hasn’t fully patched across all versions.
Affected range: iOS 18.4 – 18.7 Who that is: Users on relatively recent iPhones who updated through the 18.x cycle but aren’t on the very latest release
”Drive-By” — What That Actually Means
Both exploit kits use drive-by exploitation. This term gets thrown around a lot, but it’s worth understanding exactly what it means.
A drive-by attack is one where simply viewing malicious content — without downloading anything, approving anything, or taking any action — triggers the exploit. All you have to do is:
- Click a link someone sends you
- Visit a website that’s been compromised (even legitimate sites can serve malicious ads)
- Click on a malicious search result or sponsored ad
- Be redirected via a URL shortener
No “Allow” prompt. No app install. No admin password. The exploit runs silently in the web rendering engine.
This is possible because modern browsers are extraordinarily complex. WebKit — the engine that powers Safari and every other iOS browser — processes billions of lines of web content with milliseconds of latency. Vulnerabilities in how it handles specific HTML, JavaScript, or media content can be exploited to run arbitrary code.
The Version Discrepancy Apple Won’t Explain
Here’s something strange: Apple’s official support documentation lists only iOS 13 and 14 devices as the explicit targets of these warnings. But people running iOS 17.x are receiving the lock screen notifications.
That gap is significant. Either:
- Apple’s documentation is lagging behind internal threat intelligence
- The actual exploitation scope is broader than they’re officially acknowledging
- Apple is notifying conservatively — warning anyone below the latest version — even if exploits primarily target specific ranges
Security researchers are noting that Apple rarely discloses full technical details of active exploits, and that the discrepancy likely means the threat is being actively tracked in real-time with the scope still being determined.
The safest interpretation: if you’re not on the latest iOS, assume you’re at risk.
Who Is Most At Risk?
High risk:
- Anyone on iOS 13.0 through 17.2.1 (Coruna’s range)
- Anyone on iOS 18.4 through 18.7 (DarkSword’s range)
- Users who click links from unknown sources regularly (social media, texts from new contacts, email)
- People who use older iPhones that can’t update to the latest iOS
Moderate risk:
- Users on the latest iOS — but who haven’t restarted their device recently (some exploits persist in memory until reboot)
Lower risk:
- Users on the absolute latest iOS version with automatic updates enabled
How to Update Right Now: Step by Step
On iPhone or iPad:
- Open Settings
- Tap General
- Tap Software Update
- If an update is available, tap Download and Install
- Enter your passcode if prompted
- Keep your device plugged in and on Wi-Fi during the update
If your device can’t update:
Some older devices (iPhone 6, 6s, SE 1st gen) can’t install the latest iOS. Your options:
- Install the latest iOS version available for your device
- Consider upgrading your hardware — a device that can’t receive security patches is permanently vulnerable
- Avoid clicking links in messages or emails entirely on that device
Enable automatic updates (so this doesn’t happen again):
- Settings → General → Software Update
- Tap Automatic Updates
- Enable Download iOS Updates and Install iOS Updates
What If You’re Already On The Latest Version?
If you’re fully patched, you’re protected from these specific exploit chains. But a few things are worth doing anyway:
Restart your device. Some memory-resident exploits don’t survive a reboot. It’s a good baseline practice after any major security event.
Review your Safari browsing history. If you clicked any unusual links in the past week, make note of the domains. You can look them up in threat intelligence databases like VirusTotal.
Check for unexpected apps or profiles. Settings → General → VPN & Device Management. If you see any profiles you didn’t install, remove them.
Enable Lockdown Mode if you’re high-risk (journalist, activist, executive). Settings → Privacy & Security → Lockdown Mode. It significantly restricts attack surface at the cost of some features.
The Bigger Picture: Mobile Browsers Are the New Attack Frontier
For years, the default mental model of malware was “don’t download sketchy apps.” That model is increasingly obsolete.
WebKit and mobile browsers are now among the highest-value attack targets in the world. Here’s why:
- Every iOS app that shows web content uses WebKit. This includes not just Safari but in-app browsers in Twitter, Instagram, TikTok, and thousands of other apps. A WebKit exploit works everywhere.
- Mobile devices carry more sensitive data than ever. Banking apps, 2FA codes, emails, photos, location history — all on the same device that browses the web.
- Users trust “just clicking a link” far more than downloading an app. The psychological barrier is much lower, which is why drive-by attacks are so effective.
- Patch cycles are slower on mobile. Many users stay on outdated iOS for months — creating a large, persistent vulnerable population.
Exploit kit operators like the groups behind Coruna and DarkSword are professional outfits. They develop or purchase zero-day and n-day exploits, maintain infrastructure, and sell or rent access to whoever can pay. The campaigns hitting iOS users right now may be driven by nation-state actors, criminal groups, or both.
Three-Step iOS Security Checklist
- Update now — Settings → General → Software Update
- Enable automatic updates — so you’re always patched going forward
- Think before you click — drive-by exploits need a link click to start. Unknown senders, shortened URLs, suspicious DMs — don’t tap without thinking
Your phone is essentially a computer in your pocket with access to your entire digital life. Treat it like one.
Stay on top of mobile security news and exploit disclosures at HackerNoob.tips. If you found this useful, share it with the group chat — the person who “never updates their phone” might need it most.